Enlarge (credit: Getty) On March 29, 2022, CNN+, CNN’s take on a video streaming service,…
The US Department of Transportation has issued a recall for all Tesla Cybertrucks due to…
Enlarge (credit: Getty | David Jennings) Intermittent fasting, aka time-restricted eating, can help people lose…
Under U.S. copyright law, Internet providers must terminate the accounts of repeat infringers “in appropriate…
The Visual Affective Skills Animator, or VASA, is a machine-learning framework that analyzes a facial…
The Meta Quest 2 is a great standalone VR headset with an extensive game and…
The iconic IC device, developed by Federico Faggin, will soon be phased out, and interested…
Enlarge / Like the Beach Properties DLC itself, this property looks a bit unfinished and…
Enlarge / A cropped image showing Raw TV’s poster for the Netflix documentary What Jennifer…
BatteryInfoView shows you the current status of your laptop’s battery capacity, charge/discharge rate, voltage, as…
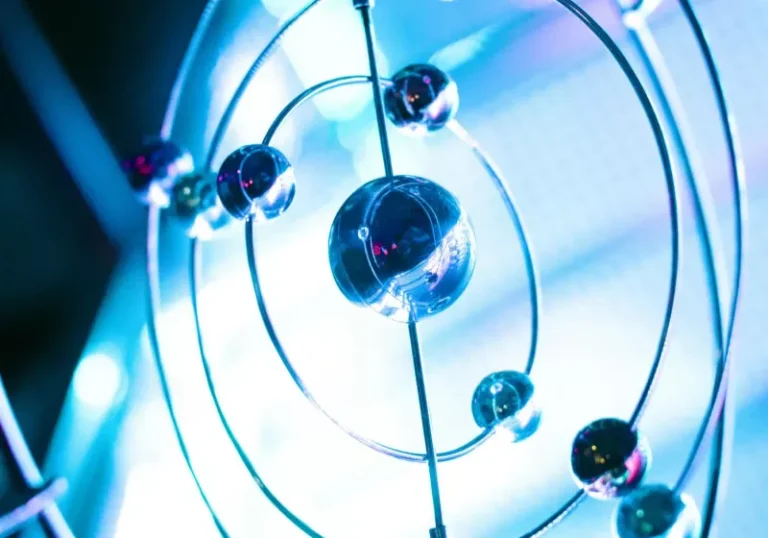
Astronomers typically do not look at these bodies when hunting for Planet Nine because they…